Password Managers 101: Why You Need One and How to Get Started
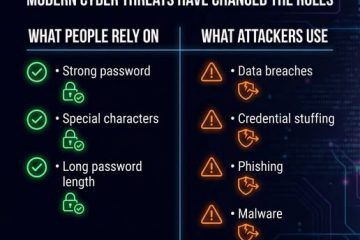
Reading Time: 3 minutesLet’s be honest: most of us have been there.A sticky note on the monitor with “Password123.”The same password reused across email, banking, and social media.Or worse—“Forgot your password?” clicked more times than you’d like to admit. In 2026, with phishing attacks, data breaches, and AI-powered password crackers on the rise, Read more…