Active Malware Threats in 2026: Types, Impact, and Defense Strategies
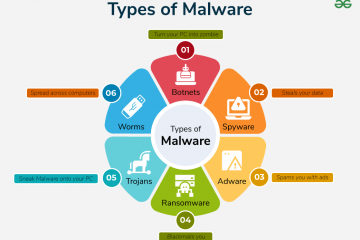
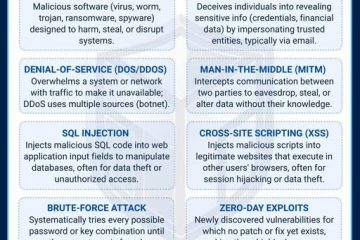
Reading Time: 3 minutesAs we move deeper into the digital decade, cyber threats continue to evolve in sophistication, scale, and intent. In 2026, threat actors—ranging from financially motivated cybercriminals to state-sponsored groups—are leveraging advanced techniques to deploy malware that bypasses traditional defenses, exploits emerging technologies, and maximizes disruption. Below is an overview of Read more…