Why Does My Computer Slow Down Over Time—Even With Plenty of RAM? (A Guide for New Tech Enthusiasts)
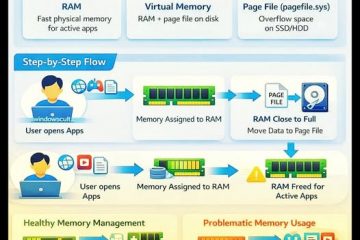
Reading Time: 3 minutesYou’ve probably heard this advice: “Your computer is slow because you need more RAM.” So you upgrade from 8 GB to 16 GB—or even 32 GB—and everything feels snappy… for a while. But months later, despite having “plenty of memory,” your laptop or desktop starts dragging again. Web pages load Read more…