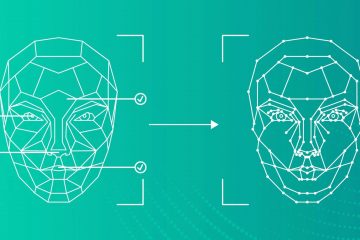
Deepfakes: How They Work, Real-World Risks, and How to Protect Yourself in 2026
Reading Time: 4 minutesIn early 2025, a video of a major European CEO appeared online, announcing a “strategic partnership” with a foreign tech firm. Stock prices surged—until the company confirmed the video was fake. The CEO never made the statement. It was a deepfake—a hyper-realistic synthetic media created by artificial intelligence. Once confined Read more…